Jul 03, 2017 MAC Address Filtering: Networks can use MAC address filtering, only allowing devices with specific MAC addresses to connect to a network. This isn’t a great security tool because people can spoof their MAC addresses. MAC Authentication: Some Internet service providers may require authentication with a MAC address and only allow a device with. A simple command line tool like GNU MAC Changer is then able to swap out the hacker's MAC address for one discovered to already be connected, allowing them to connect to the network disguised as the trusted, authorized device, granting them the same level of access. How To: Hack Open Hotel, Airplane & Coffee Shop Wi-Fi with MAC Address Spoofing Hacker Fundamentals: The Everyman's Guide to How Network Packets Are Routed Across the Web Forum Thread: Authentication Attacks 0 Replies 2 yrs ago.
MAC address filtering is one of those controversial features that some people swear by, whereas others say it’s a complete waste of time and resources. So which is it? In my opinion, it’s both, depending on what you are trying to accomplish by using it.
Unfortunately, this feature is marketed as a security enhancement that you can use if you are technically-savvy and willing to put in the effort. The real fact of the matter is that it really provides no extra security and can actually make your WiFi network less secure! Don’t worry, I’ll explain more about that below.
Apr 09, 2017 Open it and there will be all the information such the phone’s mac address and from there you can get it. Once you the victim’s mac address you are good to go with the rest of the process for hacking WhatsApp by spoofing the mac address. Listed below are all the steps involved in the procedure. A MAC address just represents the physical address of a device. They are defined by the manufacturer to uniquely identify a network device. It is easy to find someone else's MAC address if you are both on the same network, however it is not linked to your email at all and it does not harm you in any way. Sudo ifconfig WLAN device goes here ether MAC address goes here edit. This is one of the easier ways to do it but there are a lot more ways and a lot more tools that can do the same thing. Just Google 'Hack hotel wifi' and you're good to go.
On your Mac, choose Apple menu Recent Items, then choose from the list of recent servers. In the Finder on your Mac, choose Go Connect to Server, click the pop-up menu to the far right of the Server Address field, then choose a recent server. Add shared computers, network areas, and workgroups to the Finder sidebar. Select the item, then. Feb 12, 2014 Windows networks just seem to work whenever they are in the mood to do so. I am positive all of the sharing/network settings are correct. I could turn off all firewalls and make the network as open/insecure as possible to explore that. Devices never have a problem connecting to the home network to get on the internet. Is a mac network or windows network easier to hack. Jan 26, 2018 The mac can see the PC and connect to it, but from the PC side the mac is invisible. Notes: I have a windows 10 laptop connected to the same network as my office Mac. I have file sharing enabled on both devices and am able to see & connect to the laptop's shared folders/files from the mac.
However, it’s not completely useless. There are some legitimate cases where you can use MAC address filtering on your network, but it won’t add additional security. Instead, it’s more of an administration tool that you can use to control whether or not your kids can access the Internet at certain times during the day or if you want to manually add devices to your network, which you can monitor.
Why It Doesn’t Make Your Network More Secure
The main reason why it doesn’t make your network more secure is because it’s really easy to spoof a MAC address. A network hacker, which can literally be anyone since the tools are so easy to use, can easily figure out the MAC addresses on your network and then spoof that address onto their computer.
So, you may ask, how can they get your MAC address if they can’t connect to your network? Well, that’s an inherent weakness with WiFi. Even with a WPA2 encrypted network, the MAC addresses on those packets are not encrypted. This means that anyone with network sniffing software installed and a wireless card in range of your network, can easily grab all the MAC addresses that are communicating with your router.
They can’t see the data or anything like that, but they don’t really have to break the encryption to access your network. Why? Because now that they have your MAC address, they can spoof it and then send out special packets to your router called disassociation packets, which will disconnect your device from the wireless network.
Then, the hackers’ device will try to connect to the router and will be accepted because it is now using your valid MAC address. This is why I said earlier that this feature can make your network less secure because now the hacker doesn’t have to bother trying to crack your WPA2 encrypted password at all! They simply have to pretend to be a trusted computer.
Again, this can be done by someone who little to no knowledge of computers. If you just Google crack WiFi using Kali Linux, you’ll get tons of tutorials on how to hack into your neighbor’s WiFi within a few minutes. So do those tools always work?
The Best Way to Stay Secure
Those tools will work, but not if you are using WPA2 encryption along with a fairly long WiFi password. It’s really important that you don’t use a simple and short WiFi password because all a hacker does when using these tools is a brute force attack.
With a brute force attack, they will capture the encrypted password and try to crack it using the fastest machine and the biggest dictionary of passwords they can find. If your password is secure, it can take years for the password to be cracked. Always try to use WPA2 with AES only. You should avoid the WPA [TKIP] + WPA2 [AES] option as it’s much less secure.
However, if you have MAC address filtering enabled, the hacker can bypass all that trouble and simply grab your MAC address, spoof it, disconnect you or another device on your network from the router and connect freely. Once they are in, they can do all kinds of damage and access everything on your network.
Other Solutions to the Problem
But some people will still say it’s so useful to control who can get on my network, especially since everyone doesn’t know how to use the tools I mentioned above. OK, that’s a point, but a better solution to control outsiders who want to connect to your network is to use a guest WiFi network.
Just about all modern routers have a guest WiFi feature that will allow you to let others connect to your network, but not let them see anything on your home network. If your router doesn’t support it, you can just purchase a cheap router and attach that to your network with a separate password and separate IP address range.
It’s also worth noting that other WiFi security “enhancements” like disabling SSID broadcasting will also make your network LESS secure, not more secure. Another one people have told me they try is to use static IP addressing. Again, as long as a hacker can figure out your network IP range, they can use any address in that range too on their machine, regardless of whether you have assigned that IP or not.
Hopefully, this gives you a clear idea of what you can use MAC addressing filtering for and what expectations to have. If you feel differently, feel free to let us know in the comments. Enjoy!
Hey Friends, Welcome to Hackingloops. Today we will learn how to bypass MAC Address Filtering on Wireless Networks. MAC Filtering or MAC Whitelist or Blacklist is an security option provided in most routers to allow or restrict particular MAC Address to allow access or restrict the Internet. If this setting is enabled then only the Machines which are allowed by MAC Filtering can use a particular Access Point. Today we will learn how to bypass MAC Filtering on Wireless Network Routers.
Most of people are aware what MAC Address is but let me brief all to revise basics. MAC Address stands for Media Access Control Address and is a unique identifier assigned to all network interfaces. With MAC filtering you can specify MAC addresses which are allowed or not allowed to connect to the network. For many occasions this might be sufficient as a security measure which makes it a little harder to use the network when the password is even known to users. So let’s start our tutorial on how to bypass MAC Address Filtering by spoofing MAC Address.
Hacking Wireless Networks bypassing MAC Address Filtering https://sampleomg.netlify.app/best-mac-hacks-2019.html.
Steps to Bypass MAC Address Filtering on Wireless Routers :
Step 1 : Consider that we have router which has MAC Filtering Configured. Say AA-BB-00-11-22 is an MAC Address which is white listed in MAC Filtering to use the Wireless Network.
Wurst Client downloads for all Minecraft versions. Download; Tutorials; Source Code; Contact Me; Donate; Search; Minecraft Wurst Hacked Client Downloads Wurst Client downloads for all Minecraft versions. Wurst for Minecraft 1.16.1 Wurst 7.3 - AutoTotem, MountBypass, 20w28a Support. Minecraft client download free. The go-to place for free Minecraft hacks, hacked clients and cheats. The MCHACKS.net database includes many different hacks & cheats for Minecraft, all of which are completely free to download. Don't waste your time and money on premium Minecraft clients, when you.
Step 2 : Let’s login into our KALI Linux Machine and Put the Particular WIFI Adapter into Monitoring mode using AIRMON-ng, this can be done by typing below command at terminal:
airmon-ng start wlan0
Furthermore, the support provided by the officials are much better than any other emulator available, but let downs are still there.Follow the instruction for the Bluestacks Method, right after this break.1. Open BlueStacks2. Tap the Search button.3. Mac game hacker games.
Step 3 : Now it may happen some KALI Linux Process is showing some error. If yes then kill the process which KALI Linux is reporting having issues, it can be done using below command:
kill [pid]
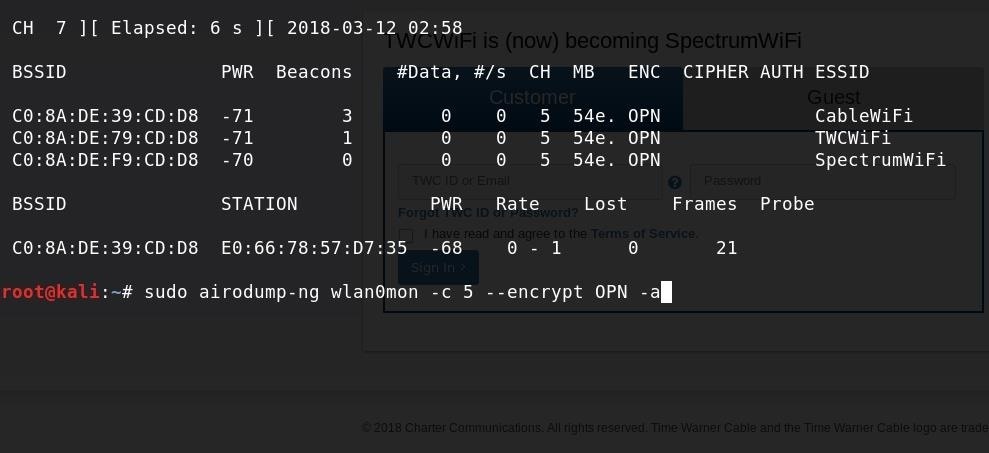
Step 4 : Now launch Airodump-ng to locate the wireless network and the connected client(s) using the following command:
airodump-ng –c [channel] –bssid [target router MAC Address] –i wlan0mon
Airodump-ng now shows us a list of all connected clients at the bottom of the terminal. The second column lists the MAC Addresses of the connected client which we will be spoofing in order to authenticate with the wireless network.
Note: You will get above list only when someone is connected to that Wireless Network already, else you will get a empty list.
Step 5 : Now we have the MAC Address, Let’s use the MacChanger to Spoof the MAC Address :
Let’s spoof the MAC address of your wireless adapter but first we take need to take down the monitoring interface wlan0mon and the wlan0 interface in order to change the MAC address. We can do this by using the following command:
Airmon-ng stop wlan0mon
Stop Mac Address Spoofing
Step 6 : Now we take down the wireless interface who’s MAC address we want to spoof with the following command:
ifconfig wlan0 down
Step 7 : Now we can use Macchanger to change the MAC address:
macchanger -m [New MAC Address] wlan0
And bring it up again:
ifconfig wlan0 up
Now that we have changed the MAC address of our wireless adapter to a white listed MAC address in the router we can try to authenticate with the network and see if we’re able to connect.
That’s it Guys! Now You are able to connect to network. Now in most cases Wireless Networks are also password protected, to hack that you can use earlier methods that i have explained in earlier tutorials.
Mac Address Spoofing Windows
Keep Learning!! Keep Connected!!