- How To Check If Mac Is Hacked
- How To Tell If My Mac Is Hacked
- How To Tell If Your Mac Is Hacked
- How To Tell If Mac Computer Is Hacked
- How To Tell If Mac Computer Is Hacked
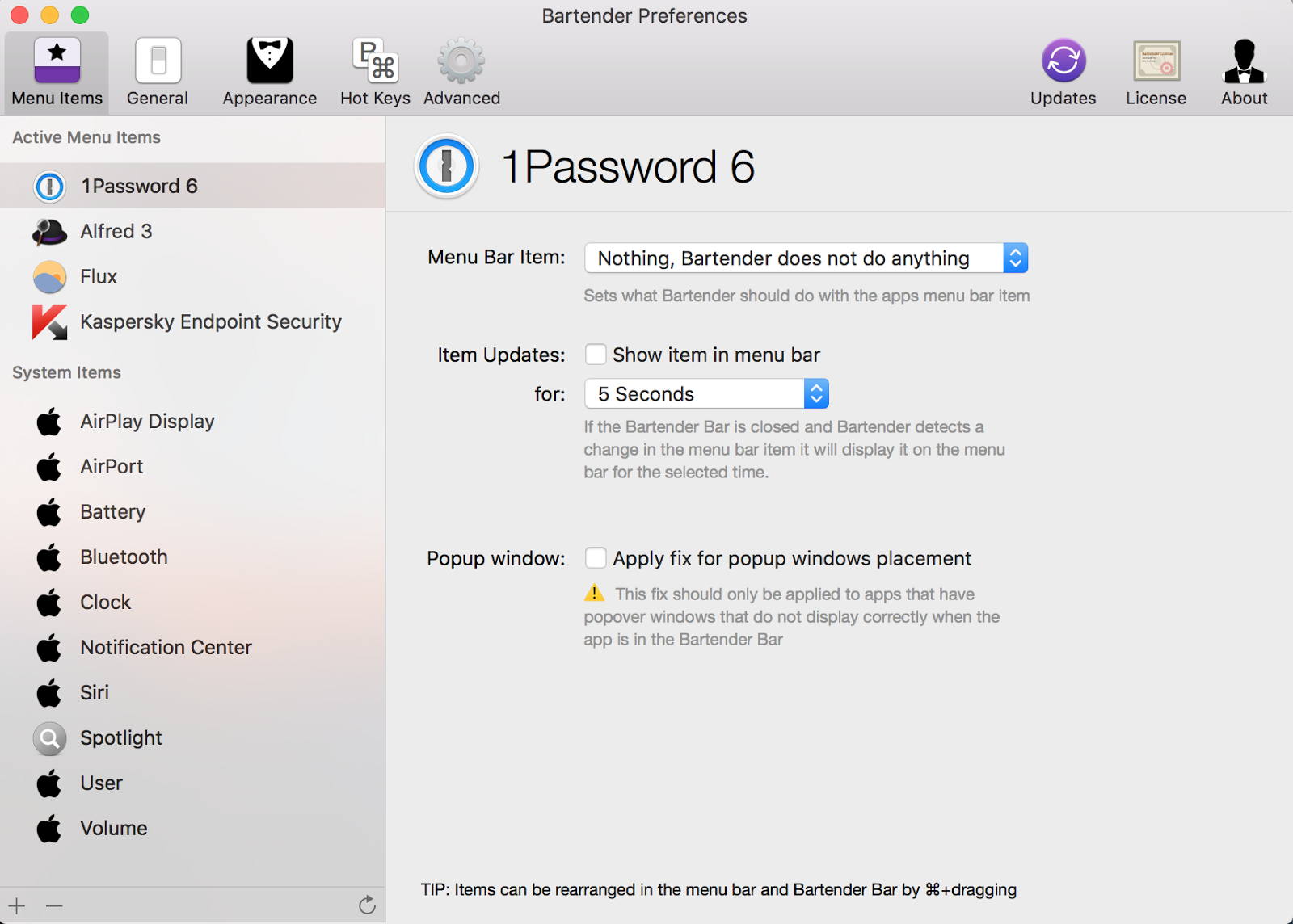
Find out if someone has accessed your MacBook's camera. Get notified when your MacBook's iSight camera is being used to keep hackers from spying on you. Jul 03, 2018 Tell them you were hacked ands that you have secured your email account again but tell them to be aware of spam and emails purporting to be from you. If someone has hacked your email, the faster you act the less damage they can do. I hope this tutorial helps you do that!
Every day we see news about computers being hacked and how the cybercriminals make money off people clueless about the protection of their assets.
For someone not very technical, it may sound as if hackers are so powerful, and the only way to hide is to shut down all devices and go off the grid completely.
However, the truth is that there are several simple things one can do to make sure that we are reasonably safe when browsing the internet without affecting our ability to access the information we need.
Whether or not someone can hack into the computer or phone through WiFi depends on a person’s proximity to the WiFi router. If a cybercriminal in the range of access to the WiFi router, they can connect to the local network and perform various attacks, such as Man In The Middle attack.
Or maybe you are using the office WiFi, and it was also hacked. And it doesn’t have to be a computer, such as a Mac or PC. Your smartphone, iPhone, or Android, which uses the WiFi can be hacked as well. Let’s see what hackers can do if they are physically connected. Jun 28, 2020 Signs that your computer has been hacked. If you think your computer has been hacked, and have Norton installed on your computer, the best option to rule out a threat infection is to perform a full system scan. However, there may be instances where the scan did not detect any threat, or you cannot perform a scan. Apr 14, 2017 I wish this would be a joke. While I was working on my MacBook with a clean install of Mac OS Sierra, suddenly my speaker were playing static noise. I could here someone clicking with a mouse.

If the hacker is outside of the WiFi range, then the way they attack will be different.
Let’s consider various scenarios of how the computer can be hacked and ways to protect your devices.
Hacking Computer Through Local WiFi
As you probably guessed, it is much easier to hack the computer, which is in close proximity to the hacker’s device.
For instance, your neighbor can connect to your WiFi and use your internet for free. Or you may connect to the free WiFi in the cafe or hotel, but someone already hacked the network, and now everyone, including you, is a potential target.
Or maybe you are using the office WiFi, and it was also hacked.
And it doesn’t have to be a computer, such as a Mac or PC. Your smartphone, iPhone, or Android, which uses the WiFi can be hacked as well.
Let’s see what hackers can do if they are physically connected to the WiFi you are using.
Man in the middle attack
If you have the internet at home from a cable, DSL, or fiber-optic provider, you have a router. Your computer does not directly connect to the internet; it sends and receives data by directing it through the router.
In layman terms, the process is the following:
- Your computer or phone finds a WiFi router.
- After submitting the correct password, the router sends back its MAC address. MAC address is an identifier of computer components, and in theory, it should be unique across billions of devices on the planet. The network card on your computer also has a unique MAC address.
- After you get the MAC address of the router, all internet activity will be going through the router. In the pic below, there is a MAC address next to each device on the local network, and the router’s address is 11:22:33:44:55:66.
When a hacker connects to the local WiFi router, it also finds the MAC address of the router. The hacker changes his computer’s MAC address to be the same as routers one (11:22:33:44:55:66 in the pic below).
Now, all devices on the local network connect to the hacker’s machine, and then the data flows to and from the router. So the hacker becomes a man in the middle (MITM).
Once this happened, the hacker can read all outgoing requests and incoming data using various tools that collect such data.
This means every time you enter a username and password on some web site or enter your credit card number, and it gets saved on the hacker’s machine. Also, every URL you are visiting also gets saved.
There are some limitations, obviously. For instance, if the website uses the HTTPS protocol (S at the end stands for Secure), all traffic is encrypted between your computer and cybercriminals will not be able to crack it (in most cases).
However, if the web site uses HTTP, all data, including the password, is in cleartext.
So, if you want to avoid your data being stolen, always check that web site is using a secure protocol (HTTPS). In the browsers, the secure protocol is usually displayed with a padlock icon next to the URL.
Never enter passwords or financial information on web sites with HTTP!
How the router can be hacked
When it comes to your home WiFi, there are three ways for someone outside to connect to the router:
- The router is not password protected
- You tell the password. For instance, you told the guest the password, or she looked it up on the router (if you didn’t change the default one)
- If the router is using an old authentication protocol
I am going to skip the first two and instead of focus on the last one. The authentication protocol used in with WiFi router is very important.
If your router is old, it is possible that it’s still using WEP protocol, then you should know that anyone who knows a little bit about hacking can hack the router literally in less than a minute.
So, if you have it enabled on your router, then go ahead and disable as I did.
What you should have is WPA2 with AES encryption. In the pic below, the authentication strength (protection from hacking) increases from top to bottom (WPA is less secure, and WPA2-PSK with AES is the most secure).
How To Check If Mac Is Hacked
Some hackers employ a dictionary attack to crack WPA protocol, but it takes supercomputers to hack it. So as long as you are not a celebrity or a billionaire, nobody will spend so many resources to break into your network.
Usually, you can connect to the home router settings by going to the local IP address, such as http://192.168.0.1/.
How to tell if someone hacked your router
One of the sure routers hacked signs is the existence of an unknown device connected to the local WiFi network.
As I explained above, in order to perform a man in the middle (MITM) attack, the hacker must connect to the WiFI network first. And if he’s connected, you can see him too.
One way to find out the connected devices is through the router settings. Some routers allow us to see all connected devices and kick them out if needed.
Another way is to use a network scanner app. For instance, I found a cool app called Fing. The app is available for almost all platforms: iOS, Android, macOS, and Windows.
It is free (with ads) and doesn’t even require creating an account in order to use it.
One cool feature they have is scanning for open ports.
For instance, when I scanned my MacBook Pro, I found that remote desktop and screen sharing features were enabled, and anyone could connect to my Mac remotely.
How to protect from a MITM attack
While it is possible to scan and find unknown devices on the home network, this approach will not work with public WiFi networks, such as the one in Starbucks or the hotel.
You would never know if the public network was compromised. In this case, the only way to protect your privacy is to use a VPN (a virtual private network).
When connected to VPN, your computer or phone creates a secure encrypted channel with the VPN server. After the connection is established, all requests go to the VPN server. The server makes all requests on your behalf and returns the results back to you.
From outside, it looks like the computer is sending some garbage to and back to the same computer. Even if the hacker collecting the information, he won’t be able to tell whether you’re connecting to Google.com or MacMyths.com.
When choosing a VPN software, follow these best practices:
- Do not use a free VPN. They have significant limitations, and you know that good things are never free.
- Test for speed. Some VPS are significantly faster than others.
- Check the provider’s reputation. Since all requests now go through the VPN, technically, the VPN server becomes a man in the middle. So choose only reputable providers.
Personally, I am using NordVPN: it’s the fastest on the market and very inexpensive. It is available for multiple platforms: macOS, Windows, Linux, iOS, and Android.
If you use my NordVPN affiliate link you get a pretty steep discount for three-year plan for up to 6 devices.
Hacking Computer Remotely
We discussed ways to hack the computers and phones through local WiFi, but I know the question that most people ask is whether hackers can connect to the home network when they are on the other end of the world (or more than a hundred yards or meters away).
Fortunately, the answer is no, someone cannot get into your home network, even if they know the password if they are outside of the range (more than 300 feet).
Also, in most cases, hackers cannot get into your computer is off (link).
However, there are other ways to get into your system remotely. Do you remember a story of Bezos’s personal data being leaked?
In his case, he received a message on WhatsApp with malware attachment. When the malware was installed on his phone, it started sending the personal data to the server abroad.
Similarly, we are all at the risk of having malware installed on our computers and smartphones. Some malware open access to the device, so the hackers can access it remotely.
Or, the malware could be a keylogger, and in this case, even having HTTPS or a VPN will not help. A keylogger will record the keys pressed on the keyboard, and if it happens to be a credit card number, then the hacker will have it.
So, how to protect the devices from malware? You need to install an antivirus program.
There is a common myth that Macs cannot have viruses, but this is not true. I was able to inject my Mac with more than 100 malware samples when testing various antimalware solution.
You can check the results of my test and recommended antiviruses in my post: Best Malware Detection App for Mac.
Every time my friends and family ask me for a recommended antivirus, I go with Norton 360. It comes with the biggest bang for the buck and provides antimalware and other security features on all platforms. And it also has its own VPN!
Conclusion
We reviewed multiple ways how someone can hack into your phone or computer through WiFi. I also listed ways to prevent this from happening, which I wanted to reiterate.
If you worry about online security, consider investing in the following tools:
- VPN software
- Antivirus program
Be very cautious when connecting to public WiFi. I’d say if you don’t have VPN installed on a laptop or smartphone don’t use public WiFi, or at least avoid making purchases with a credit card or entering passwords.
If you are interested in the topic of security, there is a great course available on Udemy about ethical hacking. The instructor teaches how to hack computers ethically and most importantly what can you do to prevent from being targeted:
Learn Network Hacking From Scratch (WiFi & Wired)Also, check my other post:
Photo credit: ©canva.com/cyano66
Last Updated on
You turn on your MacBook and feel that something is wrong: some files have disappeared, or new files were added. You wonder if someone has been watching your computer.
So, how to tell if someone is remotely accessing your MacBook? You need to check your logs, verify that no new users were created, make sure that remote login, screen sharing and remote management are disabled, and no spyware is running on your computer.
First things first. If you suspect that someone is controlling your laptop and if there is a chance that they watching you thru the webcam immediately apply a cover on laptop’s webcam. You can find my favorite webcam covers here.
What is remote access and how is it configured on MacBooks?
There are three ways to access MacOS remotely: allow remote logins from another computer, enable Screen Sharing or allow access by using Remote Desktop. Both ways are legitimate, but if you don’t remember doing any of them you need to know how to turn on and off those possibilities.
Remote login to MacOS
Computers that run MacOS as an operating system can log in to your Mac using Secure Shell (SSH). Steps to enable remote login are the following:
How To Tell If My Mac Is Hacked
- Go to System Preferences. You can get there by clicking on the apple icon on the left of the top bar. After you clicked on apple icon you will see a drop-down menu where you should click on System Preferences menu item.
- Find Sharing folder and double click. Click on Remote Login checkbox on the left.
- Now you have the option to allow access either for all user or only specific users.
Once Remote Login is enabled then users with access can use SSH to log in and browse your computer’s contents.
Access to Mac screen using Screen Sharing
If you need help from IT to make changes on your MacBook or maybe you are collaborating on a project and want to share your screen you can enable Screen Sharing. Steps to enable as follows:
- Go to System Preferences.
- Find Sharing folder and double click. Click on Screen Sharing checkbox on the left.
- Allow access either for all user or only specific users.
Now on another Mac (from which you want to access to your Mac) start Screen Sharing app. You can start it by clicking Command and Space buttons. In a popup form type Sharing and hit Enter. Type your computer name. In my case, I had to type in “dev-pros-MacBook-Pro.local”.
A new window will pop up with the shared screen of another computer. Now you can control the screen.
Remote Desktop with Remote Management
Finally, it is possible to login to a computer with MacOS by enabling Remote Desktop. Steps to enable as follows:
- Go to System Preferences.
- Find Sharing folder and double click. Click on Remote Management check box on the left.
- Allow access either for all user or only specific users.
- There will be different Sharing options where you can fine-tune the type of access to allow: observe, change settings, delete, copy and even restart the computer.
Now you can access this Mac from Apple Remote Desktop – it’s an application you can buy from Apple Store and at the time of writing it’s cost was $79.99.
If your Mac is being monitored, it will show this image (two rectangles) in the top right-hand corner near your computer time:
When that symbol appears, you will be able to tell if you are being monitored. You can also disconnect the viewer by clicking on Disconnect option:
You can also click on “Open Sharing Preferences…” which will open Sharing folder in System Preferences.
Since the question you had was if someone remotely accessing your computer then the chances are that you don’t need any of sharing capabilities mentioned above.
In this case, check all options on Sharing folder under System Preferences to make sure that nobody is allowed to access it and turn off (uncheck) all options.
Verify if new users were created
As we’ve seen already remote login or sharing options require assigning access roles to the local users. If your system was hacked it is very likely that the hacker has added a new user to access it. To find out all users in MacOS perform the following steps:
- Start Terminal app by either going to Applications and then Utilities folder or clicking Command and Space and typing Terminal in the popup window.
- In the Terminal window type:
On my laptop it listed dev1, nobody, root and daemon.
If you see the accounts, you do not recognize then they probably have been created by a hacker.
In order to find when the user account was used to log in last time type the following command into the Terminal:
last
For each account, MacOS will list the times and dates of logins. If the login to any of the accounts happened at an abnormal time, it is possible that a hacker used a legitimate account to log in.
Check the logs
It may be useful to check the system logs for any possible access issues.
In order to find a system log, click on Go option in the top menu or simultaneously click Shift, Command and G. In the “Go to Folder” popup type: /var/log and hit Enter.
Now find system.log file and scan for word sharing. For instance, I found following screen sharing log entries:
These were log entries when someone logged in to my system remotely:
Check for spyware
If you are still suspecting that spyware is running on your machine you can use a third party application like Little Snitch which monitors applications, preventing or permitting them to connect to attached networks through advanced rules. Setting up the rules for Little Snitch, however, could be complicated.
One of the common spyware applications is a keystroke logger or keylogger. Keyloggers used to be apps that record the letters you type on the keyboard, but they significantly in last years. Suffice to day that keyloggers can take screenshots every 30 seconds or even track your chat activity, including the messages sent to you.
I believe that keyloggers are much greater security threat because they are easier to install and the powerful features they offer. Check my article about keyloggers here: How to know if my Mac has a keylogger
Security Best Practices
1.Change passwords regularly
One thing you should immediately if you are suspecting that someone is logging to your system is to change your password. And the password should be complex enough so that other people wouldn’t be able to guess it. This means avoiding using things like birthdate, first or last name or relatives, house or apartment number, etc. As a rule of thumb the password must be long enough (8 – 32 characters) and include at least 3 of the following character types:
- Uppercase letter (A-Z)
- Lowercase letter (a-z)
- Digit number (0-9)
- Special characters such as ~!@#$%^&*
How To Tell If Your Mac Is Hacked
2.Enable Security Updates by clicking on “Automatically keep my Mac up to date” in Software Update folder in System Preferences.
How To Tell If Mac Computer Is Hacked
3. Install Antivirus. I received a lot of emails where people described suspicious activity on their Macs. I found that in about 60-70% cases, the culprit was malwareand not someone breaking into the computer. It’s a myth that Macs don’t get viruses. If you need proof check the next article I wrote after testing 12 antivirus programs after injecting 117 malware samples on my Mac:
How To Tell If Mac Computer Is Hacked
Last Updated on